
You are in a maze of twisty little passages, all alike...

The Worst Passwords of 2024?
November 15, 2024 Reading time: 17 minutes
NordPass has published their 2024 list of the 200 most commonly-used passwords and, apparently, many people still haven't gotten the memo about password security. Is one of your passwords on this year's list? Well, probably not. NordPass' data comes from a large database of passwords, presumably passwords that have been made public after online service data breaches. A closer look at the data gives some interesting insights into both the psychology behind passwords and websites' adherence to security "best practices." But it also raises some questions about the methodology NordPass used to generate the list. The closer I looked at NordPass' annual list, the more questions I had.
This year, NordPass' crown of dishonor goes to "123456" as the world's most common password in 2024. But is it really? In this article, I'll take a look at NordPass' data, which may not be quite what's on the label, and, just for fun, I'll compare it to some recent password data of my own, collected originally for my recent A Month of Bans article.
Read more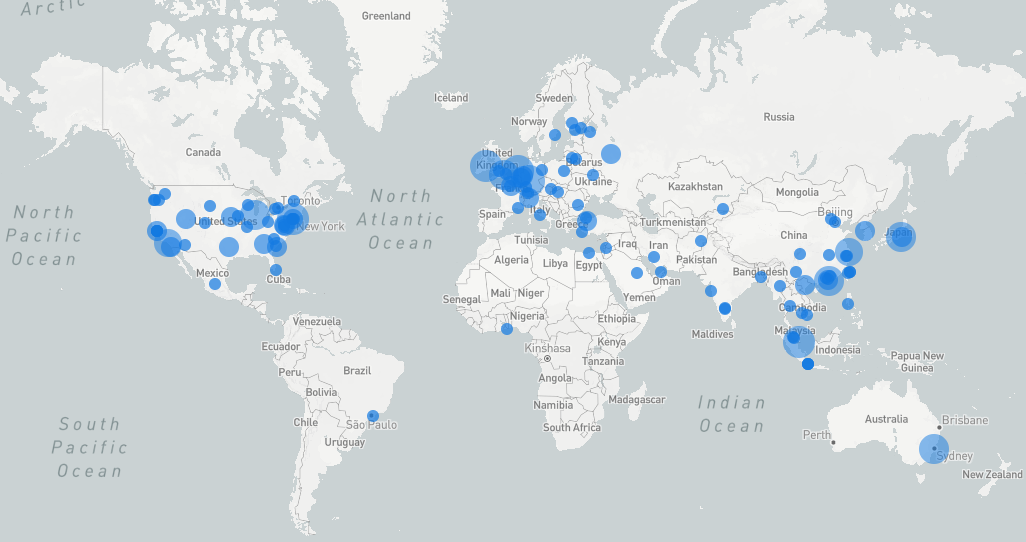
A Month of Bans: A Cybersecurity Review
November 7, 2024 Reading time: 33 minutes
If you've ever maintained a public internet server, either as a hobby or as a job, you're no stranger to random probes and port-scans from evildoers looking for trouble. You've seen brute force attempts to log in to servers or email accounts, probes for vulnerable web services, SYN floods, spammers checking for open relays, and many other attacks. If your server is on the internet, it's a target. Many hobbyist and small business systems administrators use Fail2Ban to respond to these threats. Fail2Ban is an always-vigilant process that monitors system logs and responds to perceived attacks by temporarily blocking the attacker's IP address at the firewall level.
Fail2Ban has served me well, but I wanted to gain some additional insight into the origins and behaviors of the villains behind the attacks. During the month of October, I used a custom Fail2Ban script to collect geolocation and other data about each IP address that Fail2Ban identified as malicious on three hosts, including 2 web servers and a mail server. Here are the results.
Read more
🪛 📐 TOOLBOX 🔨 🔧
📬 SPF Record WizardThe prayer is inscribed in an ancient script, rarely used today. It seems to be a philippic against small insects, absent-mindedness, and the picking up and dropping of small objects. The final verse consigns trespassers to the land ofthe dead. All evidence indicates that the beliefs of the ancient Zorkers were obscure.